I was recently tasked with creating a solution that can enforce temporary group membership on a group in Active Directory. We don’t have a Server 2016 functional level so cool new features like “Privileged Access Management” are out of the picture. I settled on some kind of scripted/automated solution.
More on Privileged Access Management here: https://docs.microsoft.com/en-us/microsoft-identity-manager/pam/privileged-identity-management-for-active-directory-domain-services
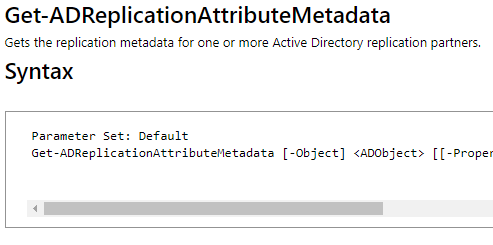
I remembered some interesting Active Directory cmdlets in Powershell from previous projects and went back and found Get-ADReplicationAttributeMetaData
Looking at the output of this command on specific objects we can see some interesting information:
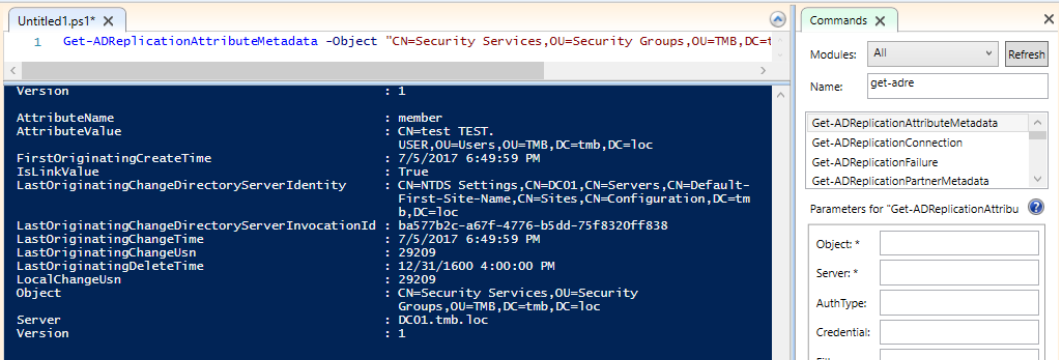
Here we can see some objects with attributeName: member. We can see all information for any member replicated to this group. Looking at the FirstOriginatingCreateTime we can see when the object was added (or replicated) into the group. Useing this information we can now compare output form this command with actual group membership. We can then compare the FirstOriginatingCreateTime to a date of our choice and decide on an action. In this case I will want to remove the object from the group.
Here is a starter script that will get the job done. I am currently using/working on a parameterized Orchestrator Runbook/Powershell script to do the same job with parameters passed to it so you don’t have to use multiple scripts for multiple groups and days to keep settings
Link: https://github.com/berendstm/TemporaryMembership
The logging on the script is somewhat detailed as we are using the transcript function within powershell. We get information like start time, hostname, powershell version, end time, script output, command output ect.

I run this script daily via a scheduled task and Orchestrator Runbook currently. You could run it just with a simple scheduled task, no Orchestrator or Runbooks needed.